In a world where hackers, computer viruses and cyber-terrorists are making headlines daily, security has become a priority in all aspects of life, including business.
But how does a business become secure? How much security is enough? How does a business know when its security level is reasonable? Most importantly what's the right amount of money and time to invest in security?
Most decision-makers do not care whether firewalls or lawn gnomes protect their company's servers but they do care about the impact security is having on the bottom line.
Before spending money on a product or service they will want to know that the investment is financially justified. There's no point in implementing a solution if its true cost is greater than the risk exposure.
In order to determine how much should be spent on security a decision-maker needs to know:
- How much do existing security problems cost the business?
- What impact would a catastrophic security breach have?
- What are the most cost-effective solutions?
- What impact will the solutions have on the business?
In order to answer these questions, measurement tools that show how security problems and expenditures impact the bottom line are needed.
The holy grail of security, from a business point of view, is to be able to calculate a return on investment (ROI) for any given security expenditure.
The search for an effective way to measure ROI for security (known in the industry as return on security investment, or ROSI) has lead to a number of interesting models, none of which have yet been accepted as the standard methodology.
ROI and ROSI defined
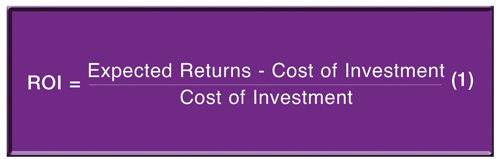
ROI is a simple yet powerful concept. 'Which of these options gives me the most value for my money?' That's the fundamental question that ROI is designed to answer. ROI is frequently used to compare alternative investment strategies.
For example, a company might use ROI as a factor when deciding whether to invest in developing a new technology or extend the capabilities of their existing technology.
To calculate ROI the cost of a purchase is weighed against the expected returns over the life of the item.
To give an overly simplistic example: if a new production facility will cost £1 million and is expected to bring in £5 million over the course of three years, the ROI for the three-year period is 400 per cent (4 x the initial investment of net earnings).
In the case of security the expected return is often interpreted as the amount of money that a company will 'save' from not having security problems as a result of the investment.
This is because security investments usually don't create value - they simply prevent bad things from happening.
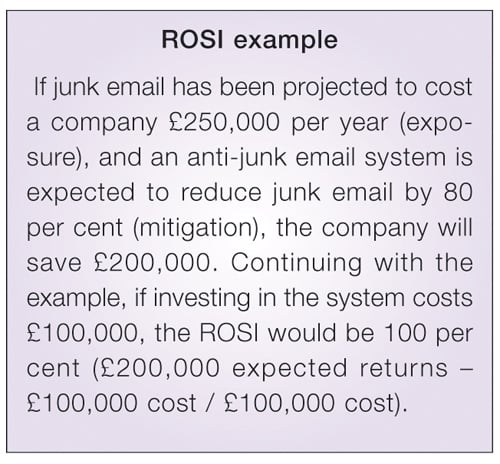
The cost of a bad thing happening is called risk exposure. A security solution mitigates that risk by some percentage. Multiplying the exposure by the percentage mitigated gives the expected return.
The trick with ROSI is in figuring out the expected returns and the true cost of the investment. In many cases an investment costs more than just what its price tag says.
The anti-junk email system in the above example will require paying for more than just the software and hardware associated with the system. Installing and configuring the system, connecting it to existing systems and training employees will result in additional costs.
It may also mean dealing with a transition period where things don't go smoothly and important emails are filed incorrectly or lost which results in wasted time and productivity.
Determining expected returns for security investments involves estimating the risk exposure and the amount a solution will mitigate the risk, neither of which is easy.
For most types of risk (auto accidents, cancer etc) the exposure and mitigating factors can be found by consulting actuarial tables built from decades of insurance claims and demographic statistics.
Unfortunately similar data on security risk does not yet exist because few companies successfully track security incidents. Security breaches that have no immediate impact on day-to-day business often go completely unnoticed.
When a breach does get noticed the organisation is usually too busy fixing the problem to worry about how much the incident actually costs.
After the disaster, internal embarrassment and/or concerns about public image often result in the whole incident getting swept under the rug. As a result of this 'ostrich response' to security incidents, the volume of data behind existing actuarial tables is woefully inadequate.
The inability to predict the total cost associated with security incidents can be sidestepped if we can find a single cost component that:
- can be consistently measured;
- strongly correlates to the overall cost;
- is significant in its own right.
It is our opinion that a security incident's impact on productivity makes for an ideal cost component that suits all three conditions.
Most importantly by using productivity as the exposure component of ROSI, security projects that improve business efficiency are promoted and those projects justified solely by fear of the unknown are eliminated.
Key point: A meaningful ROSI can be calculated by focusing on the impact security has on productivity.
The relationship between productivity and security
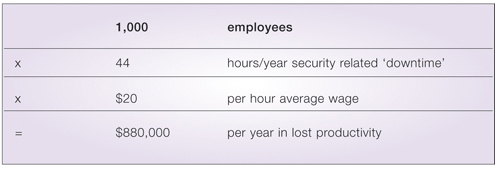
The productivity lost due to security incidents can have a serious impact on the bottom line. For many organisations the cost of lost productivity associated with a security incident is far greater than the cost of data recovery or system repair. Just ten minutes of downtime a day per employee can quickly add up to a significant amount, as illustrated in Table 1.
Productivity is not only a factor in risk exposure - it's a factor in the cost of a solution as well. Because security almost always comes at the cost of convenience, most security solutions end up creating hurdles that employees need to jump in order to do their jobs. Depending on the size and frequency of these hurdles, the lost productivity cost can seriously add up.
The situation doesn't have to be grim - it is possible for security solutions to increase productivity. This happens when side-effects of a solution eliminate other significant problems that were hampering productivity.
For example, implementing a firewall might require a network restructuring. The new structure might solve serious bandwidth problems that were previously creating extensive downtime.
With good planning most security solutions can be implemented in a way that results in an overall enhancement of productivity.
Key point: The cost of a solution must include the impact of the solution on productivity, since this number is often large enough to make or break the viability of a given solution.
Measuring productivity
How can productivity be measured? Internally, productivity is often measured using a combination of performance appraisals and profit/loss metrics.
The problem with this approach is that isolating security's impact on productivity from other factors (such as poor performance) is impossible.
Technical measurements of system downtime are also not adequate since system downtime is only relevant when it prevents someone from doing their job.
An hour of server downtime at 3am usually doesn't have a significant impact on productivity. It's much more important to measure the end-user's perception of downtime, since this directly corresponds to their productivity. Measuring employee perception of downtime can be accomplished with a survey.
If the survey is correctly constructed, there will be a strong correlation between the survey score and financial performance. Specifically if a department shows a decrease in perceived downtime, it should also show an increase in productivity on the internal balance sheets.
The key to getting consistent results from a survey that measures employee perception is to ensure that the questions are quantitative, clear and answerable without too much thought.
For example, a bad question would be, 'Estimate the amount of downtime you had this month,' since few people could answer this without logging events as they happen.
A better question is to ask, 'How often is the fileserver unavailable for more than 10 minutes (daily, weekly, monthly, rarely)?'
A person who experiences fileserver problems is unlikely to put down 'daily' unless the problem is extremely frequent.
Key point: With a good survey and scoring system for productivity, combined with external measurements of intellectual property value, it becomes possible to quantify risk exposure in a repeatable and consistent manner.
Putting it all together: The SecureMark system
The SecureMark system is a real-world implementation of the concepts put forth in this article. Its goal is to provide a trustworthy standard for security benchmarking, one that produces consistently repeatable results that are strongly correlated to financial performance.
SecureMark scores are used to compare security expenditures based on meaningful ROSI calculations.
The unique approach taken by SecureMark is its focus on productivity. Risk exposure is measured as the productivity loss due to existing security issues.
Solutions are presented that minimise this loss and therefore provide instantly realisable returns, as opposed to returns that only happen if the security solution prevents a major disaster.
Our assumption is that serious disasters are rare and hard to quantify but everyday incidents create a significant amount of aggregate loss. Solving these problems provides real returns and improves security at the same time, which has the side-effect of preventing some of those major disasters.
Not only is productivity a major factor in calculating risk exposure, it's also a significant factor in the cost of a solution.
Security solutions can have a positive, negative or neutral influence on organisational productivity. This influence can be significant and must be factored into the cost of the solution.
SecureMark can estimate the impact a given solution will have on overall productivity. This impact is factored in when prioritising underlying problems and their respective solutions.
The SecureMark scorecard gives all the factors necessary to calculate ROSI risk exposure expressed in dollars of lost productivity, and the percentage of risk currently mitigated expressed as a SecureMark score.
The analysis indicates the top problems prioritised by their impact on risk exposure and lost productivity. Likewise the solutions presented are selected based on their predicted ability to mitigate risk and minimise lost productivity.
The result is the only automated, repeatable and consistent ROSI benchmarking system available to date.
















