ITNOW's new section, Popular Computer Science (or PopCompSci) brings the most exciting stories from around the world of computer science together for a taste of the unexpected ways in which tech is impacting our lives.
AI spots crumbling concrete
To keep the public safe, a multi-functional team of building experts and AI developers have created an AI-based imaging system trained to spot problems with ageing concrete buildings.
Reinforced Autoclave Aerated Concrete — RAAC — is a lightweight concrete that was used in many buildings during the 1950s and 60s. Commonly used in roofs, sometimes in floors and often in public sector buildings, RAAC hit the headlines recently when cracking and crumbling left schools and hospitals facing spiralling repair bills and, in some cases, safety based closures.
To help building owners and operators meet their legal safety obligations, a team from Loughborough University has developed an AI-based system that can spot and access cracks in RAAC.
Professor Chris Gorse says the project involved identifying RAAC faults within NHS buildings. He said there was no unified approach to collecting data: ‘We realised that we needed to start collecting data that was less based on the manual surveying processes and more to do with what could be captured as real and accurate data. So, we started to provide the estates with a systematic process for collecting photographic records. Through this imagery, you can start to recognise what cracks are in place and, in time, we can recognise individual cracks and see if they increase or decrease.’
The digital tool uses software produced by academics within the University’s School of Architecture, Building and Civil Engineering and creates thousands of images to detect any ongoing deterioration within RAAC, highlighting the location and proposed lifespan of cracks within the concrete.
Though around 95% accurate, the Loughborough team believes — for the moment — that surveyors should use the software as an assistive technology and not as a means of replacing human hard-hat wearing experts. In collaboration, AI and human experts should be able to extend buildings’ usable lives.
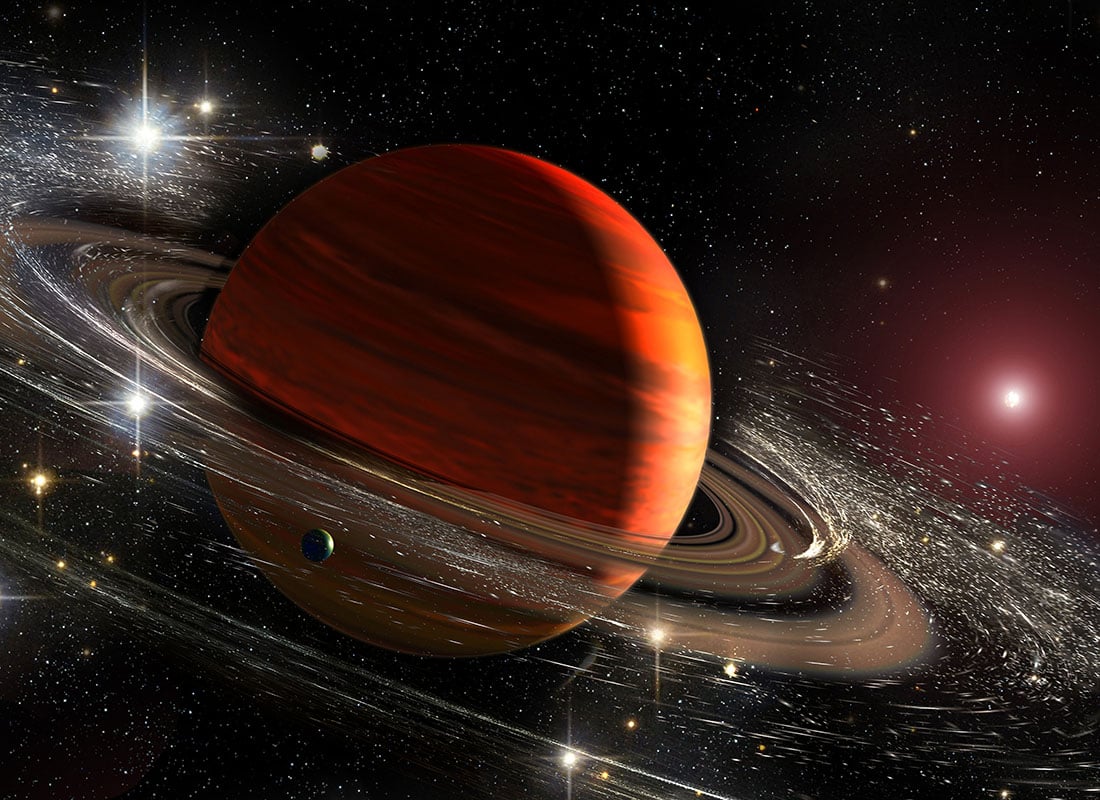
Supercomputer solves Saturn ring mystery
In collaboration with NASA, a team from Durham and Glasgow universities built a high-resolution moon-collision model that sheds new light on the origins of Saturn’s rings.
According to new research involving NASA, and Durham and Glasgow universities, Saturn’s rings could have evolved from the debris of two progenitor icy moons colliding — and this collision would have happened only a few hundred million years ago.
Offering an answer to the ring’s mysterious origin, the team used supercomputer simulations to model collisions between two moons around the same size as Saturn’s Dione and Rhea. Debris that didn’t end up in the rings could also have contributed to the formation of some of Saturn’s present-day moons.
Dr Jacob Kegerreis, a Durham University graduate who is now a research scientist at NASA’s Ames Research Center in California’s Silicon Valley, said: ‘There’s so much we still don’t know about the Saturn system, including its moons that host environments that might be suitable for life, so it’s exciting to use big simulations like these to explore in detail how they could have evolved.’
By simulating almost 200 different versions of the impact, the research team discovered that a wide range of collision scenarios could scatter the right amount of ice into Saturn’s Roche limit, where it could settle into rings as icy as those of Saturn today.
Motivated by the remarkable youth of the rings, the research team turned to the COSMA machine hosted by Durham University as part of the UK’s DiRAC (Distributed Research Utilising Advanced Computing) facility.
For you
Be part of something bigger, join BCS, The Chartered Institute for IT.
The team modelled what different collisions between precursor moons may have looked like.
These hydrodynamical simulations were conducted using the SWIFT open-source software at a resolution more than 100 times higher than previous studies, giving scientists their best insights into the Saturn system’s history.
Dr Luis Teodoro, of the University of Glasgow’s School of Physics & Astronomy, said: ‘The apparent geological youth of Saturn’s rings has been a puzzle since the Voyager probes sent back their first images of the planet. This collaboration has allowed us to examine the possible circumstances of their creation, with fascinating results.’
Thermal attacks
Password-cracking criminals could use cheap thermal imaging cameras to detect recently pressed keys. A Glasgow University team explains how and how the tech industry can protect us.
A team from Glasgow University has developed a set of recommendations designed to help protect users from thermal attacks. For criminals, the idea is deceptively simple: use a thermal imaging camera to pick up traces of heat after a user has interacted an ATM, a keyboard or a PIN pad.
Early work from the Glasgow team, headed by Dr Mohamed Khamis, found that even non-experts could guess passwords simply by looking at thermal images of a keyboard in 30 to 60 seconds.
In a paper published in the journal ACM Transactions on Privacy and Security, Dr Khamis and the authoring team, Ms Norah Alotaibi and Dr John Williamson, explained how they set out to harness machine learning to make the attack process more accurate. To do so, they took 1,500 thermal photos of recently-used QWERTY keyboards from different angles.
Dubbed ThermoSecure, the AI system proved to be very successful. Testing showed it was capable of revealing 86% of passwords when thermal images are taken within 20 seconds, and 76% when within 30 seconds, dropping to 62% after 60 seconds of entry.
Alongside designing an attack, the team also offered advice on how to defend. The team suggested that manufactures of secure input devices might add physical screens to block the contact surface from view. They also suggested that touch screens might, between users, shuffle the order in which virtual keyboards appear.
Finally, Dr Khamis added: ‘Our final recommendation is to the manufacturers of thermal cameras, who could stop attacks by integrating new software locks to prevent thermal cameras from taking pictures of surfaces like PIN pads on bank machines.’